The audit scramble: why legal teams panic at documentation requests
When regulators request documentation, legal teams scramble. GDPR fines reach €20M, but most firms cannot prove policies are current. Why the audit scramble happens.
Table of contents
An email arrives at 9:47 AM from the regulator's office. "Please provide all policies relating to data processing, sub-processor management, and cross-border transfer mechanisms — current as of today. Response required within 5 business days." The legal team's reaction is the same every time: barely controlled panic. Legal audit preparation becomes the only priority. Every firm has a version of this story. Every compliance officer has felt the cold drop in their stomach. This article is about why.

The anatomy of the scramble
If you've lived through a regulatory audit request, you already know what happens next. The general counsel sends an urgent Slack message. The compliance team starts opening every folder they can find. Someone asks, "Do we have a SharePoint for this?" Someone else replies, "We moved off SharePoint in 2023 — or did we?"
The "which version is current?" problem surfaces immediately. Three departments have three versions of the same data privacy policy. Legal drafted the original. Compliance updated it after the 2023 EDPB guidance revisions. IT security created their own version for vendor onboarding. All three versions are titled "Data Processing Policy — Final." None of them agree on sub-processor notification requirements.
Then there's the "sign once and forget" culture. A data processing agreement was approved in 2021 — before the EDPB's revised enforcement guidance on controller obligations for sub-processor monitoring. The policy references the pre-revision framework. Nobody flagged the gap because nobody was checking. The document looked fine. It just happened to be two years out of date on a point that regulators specifically examine.
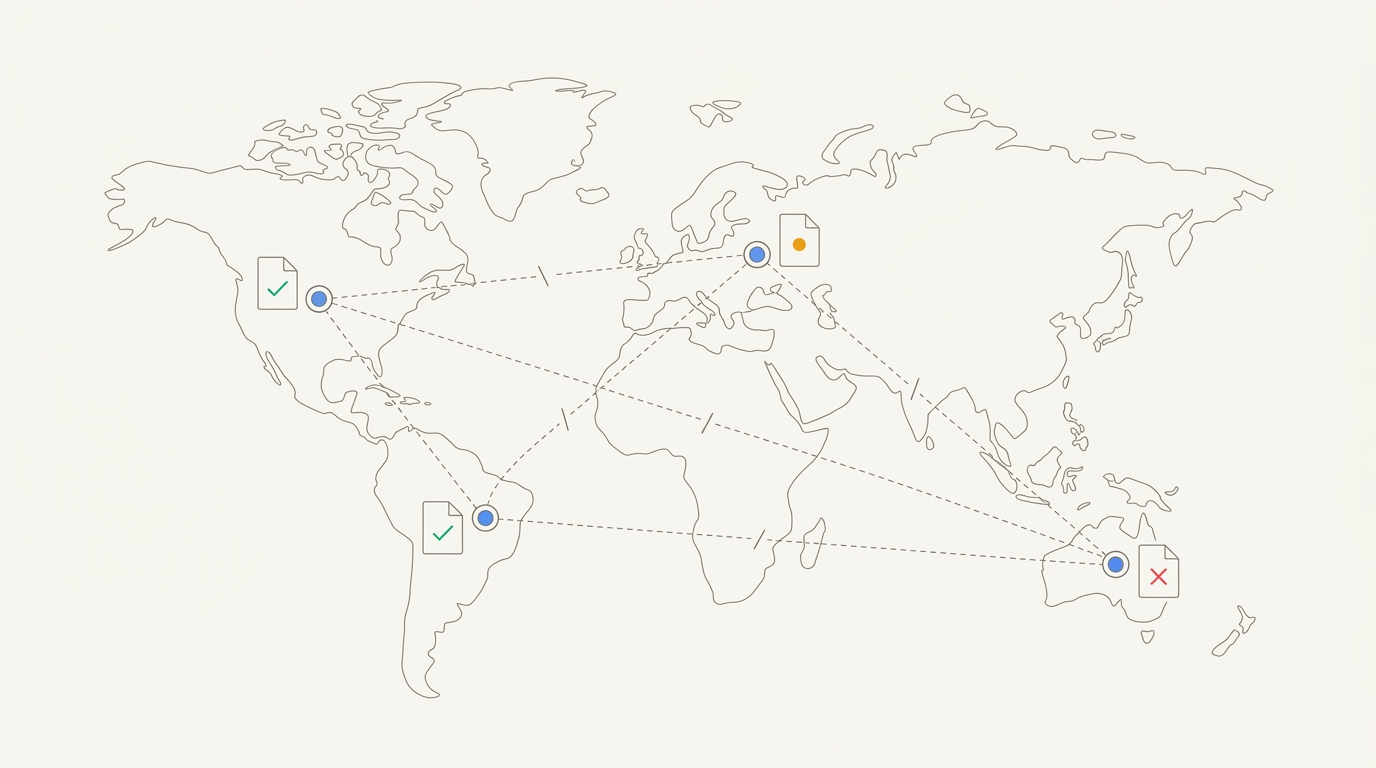
The cross-border maze compounds everything. A policy written for EU operations is being applied across APAC offices without jurisdictional adaptation. What satisfies GDPR in Frankfurt doesn't satisfy PDPA in Singapore. The California office is running on the EU version with a one-paragraph CCPA addendum that a paralegal drafted from a blog post. Nobody reviewed it. Nobody approved it.
And underneath it all sits the audit trail gap — the question that makes compliance officers lose sleep. When was this policy last reviewed? By whom? What changed? Can you prove it? Most firms can answer none of these questions with confidence. The documents exist. The proof of their currency does not.
"How do you audit internal policies before an audit?" It's a question that surfaces in legal ops communities with uncomfortable regularity, because most teams don't have a good answer.
Why the scramble happens: three systemic failures
Version chaos
Policy fragmentation isn't a people problem. It's an architecture problem.
When a data privacy policy is drafted by legal, stored in the DMS, copied to the intranet by compliance, adapted by IT security for vendor contracts, and referenced in a training deck by HR — five versions now exist across five systems. None of them are linked. None of them know about each other. When the EDPB issues new guidance and legal updates the master policy, the other four copies remain frozen in time.
This isn't negligence. It's the predictable consequence of document systems designed for storage, not synchronization. Each system works exactly as intended. The failure is that no system was designed to maintain a single, authoritative source across all of them.
The problem scales with the organization. A 50-person legal department managing policies across four jurisdictions, three business units, and two legacy DMS platforms from pre-merger operations doesn't have a version control problem. It has hundreds — one for every policy, in every system, in every office. We found this fragmentation to be nearly universal among our customers: even the most operationally rigorous legal departments have pockets of unlinked, unversioned policy documents living in systems that were never designed to stay in sync. The first-hand experience of a regulatory audit, where that fragmentation suddenly becomes a five-day emergency, is what typically drives the change.
Silent regulatory drift
Regulations don't stand still. GDPR enforcement guidance evolves. EDPB opinions reshape controller obligations. National data protection authorities issue rulings that change compliance requirements. But the policies referencing those regulations? They stay exactly where they were when someone last opened them.
A sub-processor management policy approved in 2021 may reference the pre-revision GDPR framework for cross-border data transfers. The Standard Contractual Clauses (SCCs) were substantially updated by the European Commission — the old SCCs expired, new ones imposed additional requirements for transfer impact assessments. If the policy wasn't updated to reflect those changes, the firm is operating under a framework that no longer exists.
Nobody notices because the policy looks normal. It has the right title. It sits in the right folder. It references real regulations. The problem is that those references are to the 2021 version of a regulatory landscape that has since shifted beneath them.
The cross-border problem
What's compliant in Frankfurt isn't compliant in Singapore. What satisfies CCPA in California doesn't satisfy the UK's post-Brexit data protection regime. And the gap between these frameworks isn't narrowing — it's widening.
As research published in the International Journal of Law Management & Humanities documents, multinational organizations face complex requirements for cross-border data transfers including adequacy decisions, SCCs, and Binding Corporate Rules (BCRs). Each mechanism carries different obligations, different documentation requirements, and different enforcement risks.
A legal department managing a single data processing policy across EU, US, UK, and APAC operations isn't managing one policy. It's managing four — each with jurisdiction-specific requirements that diverge on consent standards, breach notification timelines, data subject rights, and cross-border transfer mechanisms. Most firms treat this as one policy with regional footnotes. Regulators treat it as four separate compliance obligations.
What this actually costs
The consequences of compliance documentation chaos aren't theoretical. They're measurable — in fines, in resources, and in the structural pressure crushing legal departments.
GDPR non-compliance fines can reach up to €20M or 4% of global annual revenue, whichever is higher (GDPR Regulation). These aren't ceiling figures reserved for the worst offenders — they're the statutory maximum that regulators can and do apply when organizations cannot demonstrate policy compliance. The inability to produce current documentation during an audit doesn't just look bad. It constitutes evidence of inadequate compliance infrastructure.
The resource pressure makes preparation harder, not easier. According to the 2025 CLOC State of the Industry Report, 83% of legal departments expect demand to increase, while 63% cite workload and resource bandwidth as their top challenge. Teams are being asked to do more — more compliance monitoring, more cross-border coordination, more regulatory response — with the same or fewer people.
And the budget isn't growing to match. The 2024 ACC Chief Legal Officers Survey found that 42% of legal departments received cost-cutting mandates. More regulatory obligations. Fewer resources. Smaller budgets. The math doesn't work — and audit preparation is where it breaks down most visibly.
Meanwhile, the regulatory landscape is becoming more complex, not simpler. The EY Law General Counsel Study 2025 found that external disruptors — geopolitical shifts, regulatory pressures, and emerging technology — create the greatest challenges for legal departments, with only 25% prioritizing GenAI as a strategic tool. Most legal departments are still responding to regulatory complexity with manual processes and institutional memory.
And the regulatory expectations are explicit. The EDPB's opinion on controller obligations makes clear that controllers must continuously review sub-processor protections — the "sign once and forget" approach to data processing agreements is no longer acceptable. Regulators expect living documentation, not archived approvals.
The audit readiness checklist most firms fail
Before the next regulatory request arrives, every legal department should be able to answer five questions:
-
Can you produce every active policy within 1 hour? Not within a week. Not after searching five systems. Within 60 minutes, can you assemble every current, approved policy relevant to the regulator's request?
-
Can you show version history and approval dates for each? Not just the current document — the full history. When was it created? When was it last revised? Who approved each version? What changed between versions?
-
Can you demonstrate which regulatory framework each policy addresses? Can you map every policy to the specific regulation, directive, or enforcement guidance it implements? Can you show that mapping is current?
-
Can you prove policies are consistent across jurisdictions? If you have a data processing policy for EU operations and one for APAC, can you demonstrate they don't contradict each other on material points?
-
Can you identify which policies reference regulations that have been amended since approval? Can you flag, right now, every policy in your system that cites a regulatory framework that has changed since the policy was last reviewed?
Most firms fail on three or more of these five. Not because they lack competent lawyers or compliance professionals — but because the systems they use were designed for storage, not for proving policy currency, tracking regulatory drift, or maintaining cross-jurisdictional consistency.
Where AI-powered knowledge management fits
Our customers in legal departments describe the same gap: they can find the document, but they can't prove it's current. When we deployed Mojar with compliance teams, the most common first reaction is relief — not at the search capability, but at the ability to answer question five above in minutes rather than hours.
The difference between a DMS and a knowledge management platform maps directly to audit readiness:
| Traditional DMS | AI-powered knowledge management |
|---|---|
| Stores policies as files | Tracks policies as living documents with version lineage |
| Retrieves by filename or metadata | Queries semantic content across all policy versions |
| Shows what's stored | Flags what's outdated against current regulatory frameworks |
| Requires manual consistency checks | Detects cross-jurisdictional contradictions automatically |
| Produces documents on request | Maintains continuous audit readiness |
| No staleness detection | Proactively alerts when referenced regulations are updated |
In practice, teams that have gone through an audit with a properly maintained knowledge system describe the experience as qualitatively different. Our approach at Mojar is to treat audit readiness as a continuous state, not a periodic scramble. We've seen teams go from a five-day scramble to a two-hour response time after deploying a properly maintained knowledge system — not because the documents changed, but because the system could now prove they were current. We recommend that legal departments think about compliance documentation the same way they think about financial controls: something that requires ongoing maintenance, not annual cleanup. Our platform is built on this premise: that proving compliance is as important as achieving it, and that the two goals require different infrastructure.
The shift: from storing policies to proving compliance
The problem isn't lazy teams. It's that traditional DMS and intranet systems were designed for a different purpose. They store documents. They organize files. They control access. What they don't do — what they were never designed to do — is answer the question: "Is this policy still current, and can I prove it?"
A new category of AI-powered knowledge platforms is emerging that approaches compliance documentation as a living system rather than a static archive. These platforms don't just store policies — they actively monitor for regulatory drift, flag when documents reference outdated frameworks, detect inconsistencies across jurisdictions, and provide instant retrieval with full audit trails.
The technology uses retrieval-augmented generation (RAG) to go beyond keyword search. Instead of searching for filenames or metadata, these systems understand the semantic content of policies — enabling queries that cut across the entire document corpus. They can surface every policy referencing a specific regulatory framework, identify which of those references are outdated, and flag contradictions between policies that were drafted independently by different teams in different offices.
This isn't about replacing lawyer judgment. These systems retrieve, flag, and surface. Lawyers review, verify, exercise judgment, and decide. The value isn't automation — it's visibility. It's the difference between hoping your policies are current and knowing they are, with evidence. Unlike traditional DMS platforms, which treat documents as static assets, these systems treat policies as living documents that need to be validated against the current regulatory environment on an ongoing basis.
For a deeper look at how RAG technology works in legal knowledge management, see RAG for Law Firms: The Complete Guide. And for more on the foundational challenge of keeping legal knowledge bases trustworthy, see "Is This the Latest Template?" Why Law Firm Knowledge Bases Fail.
How audit-ready is your legal department? If the answer gives you pause, request a demo — before the next email arrives at 9:47 AM. Or start a free trial to see how Mojar handles your actual compliance documentation.
Bob Mojar is the founder of Mojar. He leads product development and works directly with the legal teams that deploy the platform.
Frequently Asked Questions
Legal teams struggle because policies live in multiple locations — DMS, intranet, email, local drives — with different teams maintaining different versions of the same policy. Nobody is certain which version reflects the approved state, and there's no systematic way to prove when policies were last reviewed, by whom, or what changed.
GDPR non-compliance fines can reach up to €20M or 4% of global annual revenue, whichever is higher. Controllers must continuously review sub-processor protections — the 'sign once and forget' approach is no longer acceptable under the EDPB's enforcement guidance.
Maintain a single source of truth for all policies with version history, implement automated staleness detection to flag outdated regulatory references, and ensure every policy can be retrieved with its full audit trail in minutes, not days. The goal is continuous audit readiness, not scrambled preparation.
Multinational legal departments must maintain consistent policies across EU, US, UK, and APAC while ensuring local compliance. A GDPR-compliant data processing policy that works in Germany may conflict with requirements under Singapore's PDPA or California's CCPA, requiring jurisdictional adaptation that many firms fail to maintain.
AI can query across all policies, flag outdated regulatory references automatically, identify inconsistencies across jurisdictions, and provide audit trails showing when documents were last reviewed. AI retrieves and flags — humans verify and decide. The technology enables continuous monitoring at a scale that manual review cannot match.
83% of legal departments expect demand to increase, and 63% identify workload and resource bandwidth as their top challenge (2025 CLOC State of the Industry Report). Meanwhile, 42% received cost-cutting mandates (2024 ACC CLO Survey). More work, fewer resources — and regulatory complexity is only increasing.
